Your challenge. Turn security constraints into value adding opportunities.
In an increasingly unstable environment marked by intensified threats, show confidence and secure your shareholders interests.
Make security your second skin, simultaneously flexible and durable. Make it supports the movements of your company. Security facilitates and gives assurance to every evolution, innovation and development. Making them sustainable.
Security is key to any successful digital transformation project. Security is a very broad field, encompassing technical, functional and organisational constraints, and, as such, requires specific expertise and skills.
Security can and should rely on the services offered by the AWS Cloud and automation to build robust and resilient environments, protect the data hosted in these new environments as well as possible, structure the DevSecOps approach, and optimise the added value of the security function in organisations.
To better understand our views on security in the Cloud, watch the webinar: “The AWS Cloud for your Security Revolution” and read our article entitled “Security in the Cloud: Four Convictions“.
How we do it Embrace the unpredictable.
Efficiently respond to threats with a clear security strategy.
Define eligibility requirements for your cloud projects, prioritize actions, update your policies framework and optimize your security processes. Draft an ISS Plan, permanent control plan, architecture patterns.
Enhance your cloud compliance monitoring.
Set up tooling and processes, automate controls, perform punctual PF and CI/CD audits and set-up remediation plan (GDPR, PCI-DSS, ANSSI & Cloud Security Alliance guidelines…). Conduct an audit of compliance with internal rules and external standards (GDPR, PCI/DSS, ISO 27001, AWS best practices, AWS WAF, AWS CAF Security Pillar, CIS, CSA, etc.)
Build resilient projects with personalized security approaches.
Work together with architect and DevOps teams to natively integrate security best practices in all your cloud projects: Build a heavy-duty and resilient cloud environment. Control and protect your strategic data. Define and implement a remediation plan. Support the roll-out of Landing Zones and secure CI/CD chains. Deliver secured applications faster. Empower your users with the proper identity & accesses.
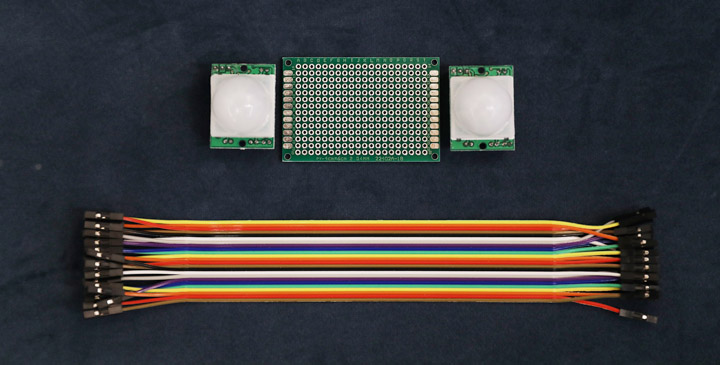
Deploy security Solutions
Native managed services (filtering and interconnections, encryption and HSM, logging and monitoring, etc.) and third-party solutions (secret managers, vulnerability scans, log management, etc.). Implement continuous Cloud compliance control chains.
Our Security Offers
Define your Cloud Security Strategy
Define a Cloud Security Strategy aligned with DevSecOps philosophy.
HARPO : Security Audit on AWS
Quickly and efficiently audit your security on AWS environnements.
Deploy Continuous Security Controls on AWS
Deploy Security Controls without limiting your Cloud & DevOps Agility.

Our Customers.
We work with organisations in all sectors, including financial services, energy and utilities, business services and manufacturing, consumer and leisure services, and transport.
Regardless of our client’s activity and size, we are able to provide end-to-end support — from scoping to implementation — to help secure Cloud and CI/CD components. Throughout the process, we transfer knowledge to the customer teams to enable them to adopt and take ownership of the DevSecOps approach. Having all stakeholders adopt this approach ensures that security issues are taken into account on a daily basis at each BUILD stage and each RUN activity. This guarantees optimum maintenance in secure conditions (e.g. in particular through automation, continuous monitoring and a permanent watch on good safety practices).
Talk to us.
Eager to work in total confidence and inspire trust?
Every change starts with a discussion.
AWS provides a secure infrastructure built to meet the highest security standards. Its architecture has been designed to protect against all types of threats, from those posed by cyber attacks to natural disasters.
To monitor, protect and maintain the underlying infrastructure 24/7, AWS uses automation as well as layered, redundant controls, continuous checks and frequent tests.
Under its Shared Responsibility Model, AWS is responsible for the security of the Cloud. This covers both the software (including computing, storage, databases, and networking) and hardware aspects of AWS. You are responsible for the security of the applications, customer data, operating systems, and networks you deploy on the Cloud.
Put another way, AWS secures the AWS Cloud environment whereas you, the customer, ensure the security of what you put into it. This distribution of responsibility allows you to remain agile and autonomous when it comes to managing the security controls of the processes you run on AWS.
There are several built-in AWS security monitoring tools that provide account security and protection for Cloud applications and workloads. These services can be broken down into six different categories:
- Identity and access management
- Detection
- Network and application protection
- Data protection
- Incident response
- Compliance
AWS Identity and Access Management (IAM) is a free, built-in AWS cloud security tool that allows you to manage permissions for various resources and services on your cloud platform. You can decide who can do what, and under what conditions. It also makes it easy to securely scale your operations.
Other available AWS identity and access tools include AWS Single Sign-On, AWS Directory Service, AWS Resource Access Manager, AWS Organizations, and AWS Control Tower.
From automating security checks and vulnerability management to tracking user activity and providing security management for Internet of Things (IoT devices), AWS security detection tools like AWS Security Hub, Amazon GuardDuty and AWS Cloud Trail are there to alert you and protect your platform the second they detect problems.
To improve your overall network security or to filter traffic to and from your cloud environment, AWS cloud security tools such as the AWS Network Firewall and the AWS Web Application Firewall (WAF) provide great protection.
For scalable solutions that find and protect your sensitive data or an easier way to manage your platform’s SSL and TLS certificates, AWS offers you data protection services like Amazon Macie, AWS Key Management Service (AWS KMS), and AWS Certificate Manager that can meet your needs.
Should AWS detect suspicious activity, Amazon Detective and AWS Elastic Disaster Recovery give you a closer look at possible security issues and allow you to efficiently and affordably recover AWS your applications.
You can ensure your AWS platform meets compliance standards with the help of the free AWS Artifact tool. You can also take things a step further by using the AWS Audit Manager to perform continuous, automated audits.
Not sure which AWS security monitoring tools are right for your company? Long-standing AWS partner Partner Devoteam A Cloud is here to help. Get in touch no
AWS uses encryption and key management along with threat detection services to secure data in their infrastructure. Through the continual monitoring of network activity and account behavior, AWS is able to identify threats and protect your data and workloads in the Cloud.
Cloud security architecture is the set of tools, technologies, strategies, and practices designed to protect workloads, data, and systems within a cloud platform. It serves as a roadmap for configuring a secure and stable cloud environment.
A solid cloud security architecture strategy should be fully integrated into your platform, meaning that it needs to be developed early on in the planning and design phases.
Important elements of cloud security architecture include physical infrastructure security, access management, methods and validations for ensuring the ongoing protection of applications and data, and the rules and regulations for meeting security compliance standards.
The goal is to anticipate and minimize risk while building a resilient and secure cloud environment.
For help setting up a secure AWS application, start now with Devoteam A Cloud.